With the advent of digitalization, the world has become a highly interconnected place, which makes cybersecurity one of the most important factors that organizations and even ordinary people should take into account. Nowadays, cyberattacks have become more sophisticated and widespread; therefore, it is crucial for organizations to be proactive and not reactive when it comes to protecting their systems. It is here that ethical hacking comes to help. Ethical or white-hat hackers employ special tools to find vulnerabilities that might be exploited by attackers, making sure no breaches occur.
What Are Ethical Hacking Tools?
As its name suggests, ethical hacking tools are software applications or platforms utilized for securing computer systems and networks. In contrast to malicious hacking tools, ethical hacking ones are utilized lawfully and responsibly, enabling hackers to ensure systems’ safety by simulating actual attacks.
The list of functions that such tools can perform is pretty broad and includes network scanning, assessment of vulnerabilities, password cracking, analysis of wireless security, and website and application testing.
Types of Ethical Hacking Tools
In order to comprehend the importance of the above-mentioned tools, it is important to classify them according to their functions:
-
Network Scanning Tools
Network scanning tools assist in detecting active nodes, open ports, and other running services within a network. This information is vital when assessing potential ways of accessing the network.
As such, network scanning tools are used to create the maps of networks in order to detect weak spots within the latter and fix them accordingly.
-
Vulnerability Assessment Tools
Vulnerability assessment tools scan computers or entire networks for security vulnerabilities and misconfigurations, which should be eliminated.
Such tools allow for continuous monitoring of network vulnerabilities and are necessary for the successful maintenance of cybersecurity.
-
Password Cracking Tools
Although the use of secure passwords might seem to be obvious enough for today’s world, it remains an extremely popular source of cybercrime and vulnerability. As such, ethical hacking uses password crackers to crack the weak passwords and make sure that there are no further problems associated with them.
-
Web Application Testing Tools
The growing popularity of web applications makes their protection extremely important. Web application testing tools find such vulnerabilities as SQL injections, cross-site scripting (XSS), and weak authentication methods.
These tools assist developers in creating robust software by revealing weaknesses in the design process and during testing.
-
Wireless Network Tools
Wireless networks are especially susceptible to attacks because they are easy to access. Wireless network testing tools analyze the strength of encryption protocols, unauthorized access points, and network configurations.
These tools are extensively used in Wi-Fi network protection in corporate and public settings.
-
Exploitation Frameworks
Exploitation frameworks give ethical hackers an opportunity to exploit system vulnerabilities by simulating real-world attacks. They can assess the risk of exploiting the discovered weakness and the consequences of a potential attack.
These tools require special skills and experience.
Popular Ethical Hacking Tools
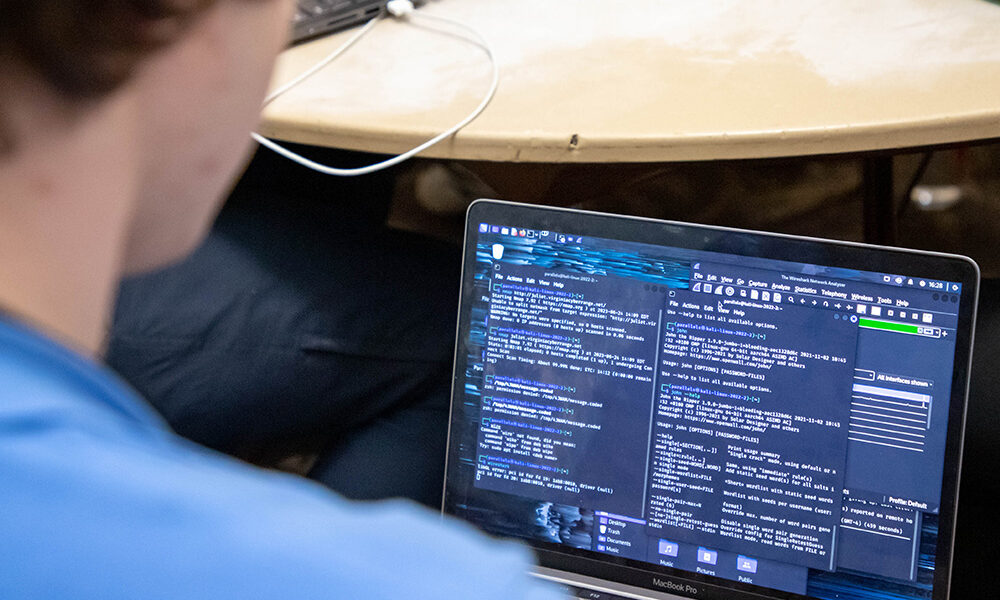
The following are some of the most popularly used tools for ethical hacking that have stood out because of their efficiency and usability:
Nmap (Network Mapper): This is a network scanner used to discover network devices, services, and vulnerabilities on networks.
Metasploit Framework: This is a penetration testing framework used to develop and implement exploits against targets.
Wireshark: This is a packet capture tool that analyzes network traffic. It can be used to analyze captured network traffic in real-time or from pre-recorded files.
Burp Suite: This is a web application security testing platform. This is a platform commonly used by penetration testers to find vulnerabilities in web applications.
John the Ripper: This is a password cracking tool used to analyze passwords. This can help determine the strength of passwords used to protect web applications.
Aircrack-ng: This is a Wi-Fi security testing tool suite.
Importance of Ethical Hacking Tools
Ethical hacking tools are instrumental in enhancing cybersecurity. The following are the reasons why they are important:
Proactive Approach
In addition to responding to attacks, organizations can find and address their weaknesses beforehand. This strategy greatly lowers the likelihood of cyberattacks.
Vulnerability Assessment
Through the use of ethical hacking tools, organizations can assess their security levels and rank their vulnerabilities depending on their significance.
Compliance
Certain industries have strict guidelines for ensuring cybersecurity among companies. These include GDPR, HIPAA, and ISO standards. Ethical hacking tools are helpful in meeting these requirements.
Prevention of Losses
It is always cheaper to prevent an attack than to deal with its effects. Hence, ethical hacking tools help save money, prevent reputation damage, and other losses that may arise from cyberattacks.
Ethical Issues and Guidelines
Although ethical hacking tools are vital, their misuse can bring significant risks. Therefore, ethical hackers should abide by some rules when utilizing these tools:
Always seek permission before testing a network.
Avoid employing hacking tools for unauthorized reasons.
Safeguard any sensitive information obtained during testing.
Disclose vulnerabilities responsibly to prevent abuse.
Ethical hackers should uphold a high code of ethics to earn public trust.
Challenges in Utilizing Ethical Hacking Tools
Not withstanding these merits, however, ethical hacking tools do have their limitations:
Technical Sophistication: Not all of these tools are easy to master.
Vulnerability False Positives: They might identify issues that do not pose an actual threat.
Regular Updating Needed: With ever-changing cyber threats, regular updates are necessary.
Possible Legal Ramifications: These tools can only be used legally with appropriate authorization.
To make sure these challenges do not pose a problem to one’s security, companies should provide their experts with necessary education.
The Future of Ethical Hacking Tools
With cyber threats becoming increasingly sophisticated, so do the means of combating them. New developments in artificial intelligence and machine learning have allowed to add even more functionality to ethical hacking tools.
These tools can now identify patterns, predict threats, and assess vulnerabilities in an automated fashion thanks to the integration of AI and ML features.
Furthermore, cloud security and Internet of Things (IoT) security have become major focuses in developing cybersecurity tools.
Conclusion
The importance of ethical hacking cannot be overstated – these tools play a crucial part in cybersecurity.
Ethical hacking tools are going to play an important role as long as cybersecurity is one of the most important issues in today’s world of digitization, providing greater security and safety for all users.